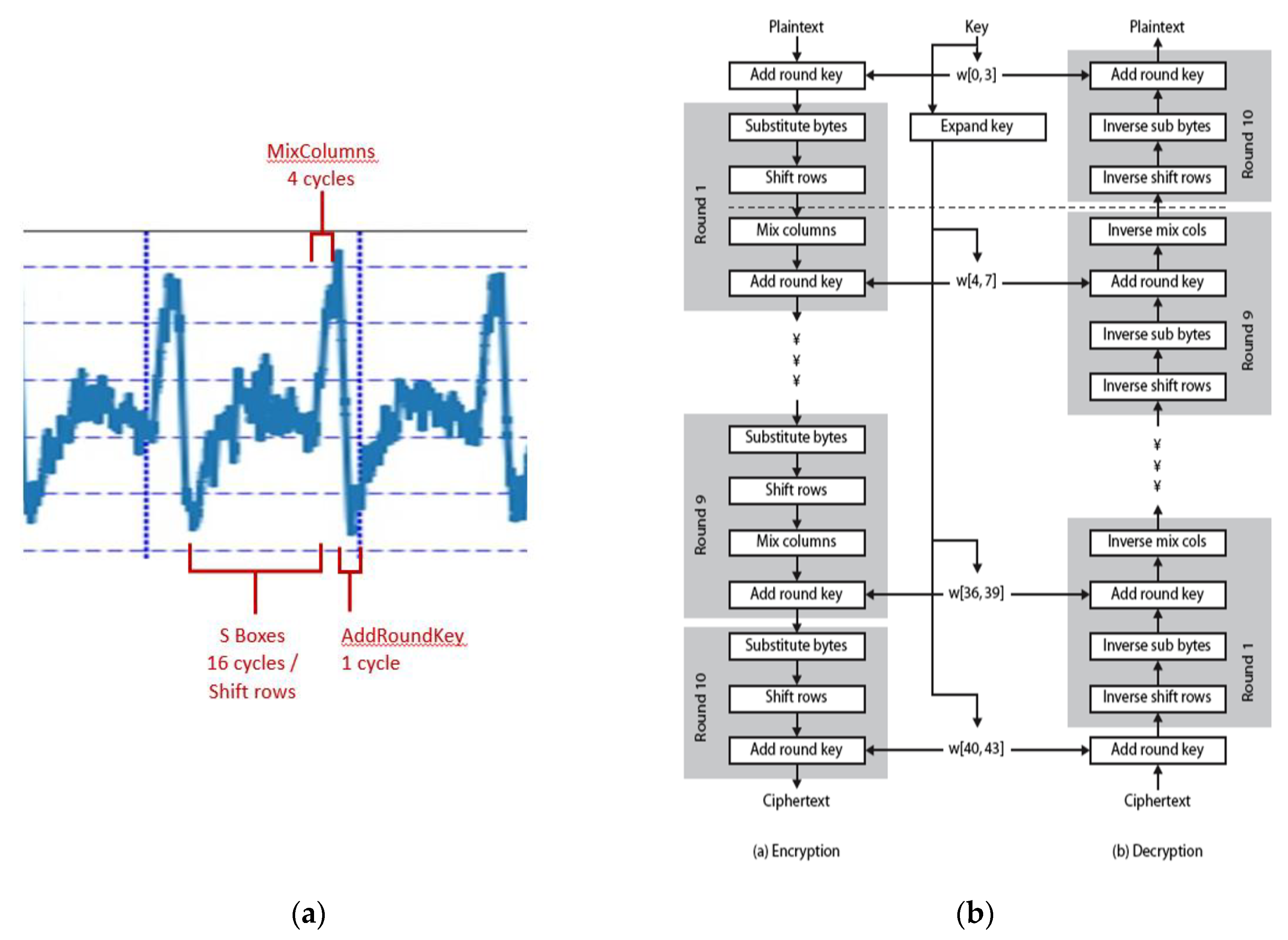
Cryptography | Free Full-Text | Power Side-Channel Attack Analysis: A Review of 20 Years of Study for the Layman

Defining the Scope of Exposome Studies and Research Needs from a Multidisciplinary Perspective | Environmental Science & Technology Letters
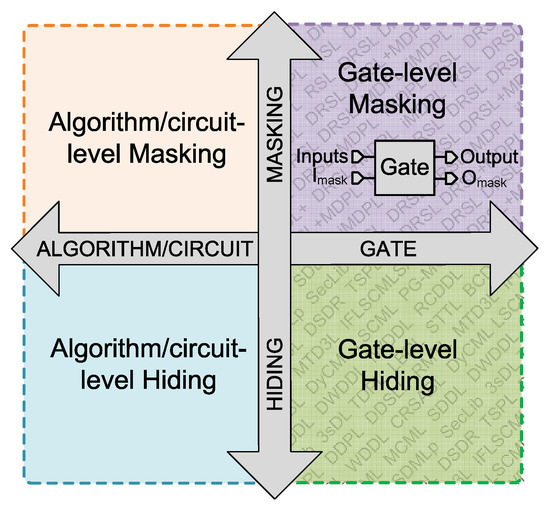
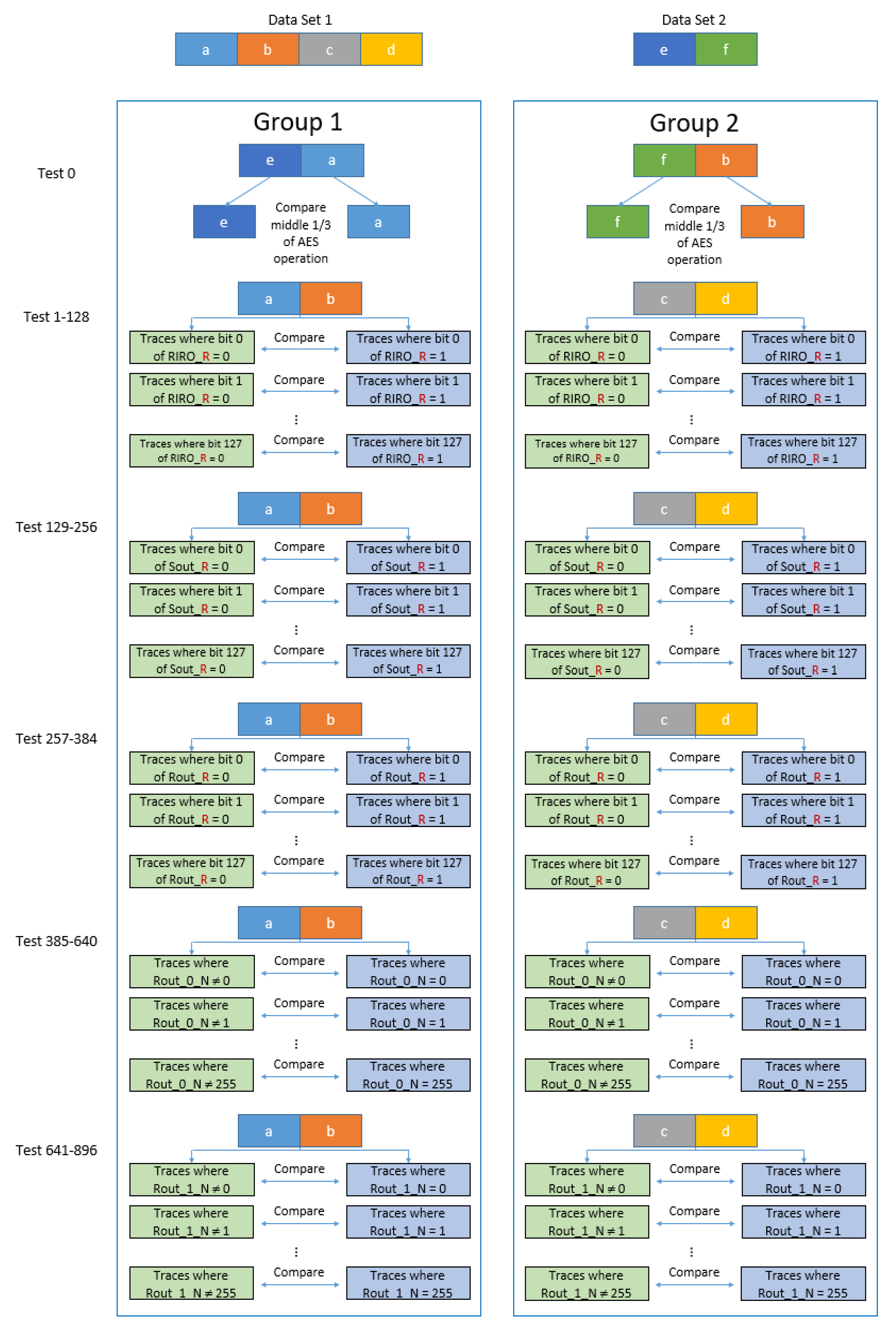
Applied Sciences | Free Full-Text | Gate-Level Hardware Countermeasure Comparison against Power Analysis Attacks
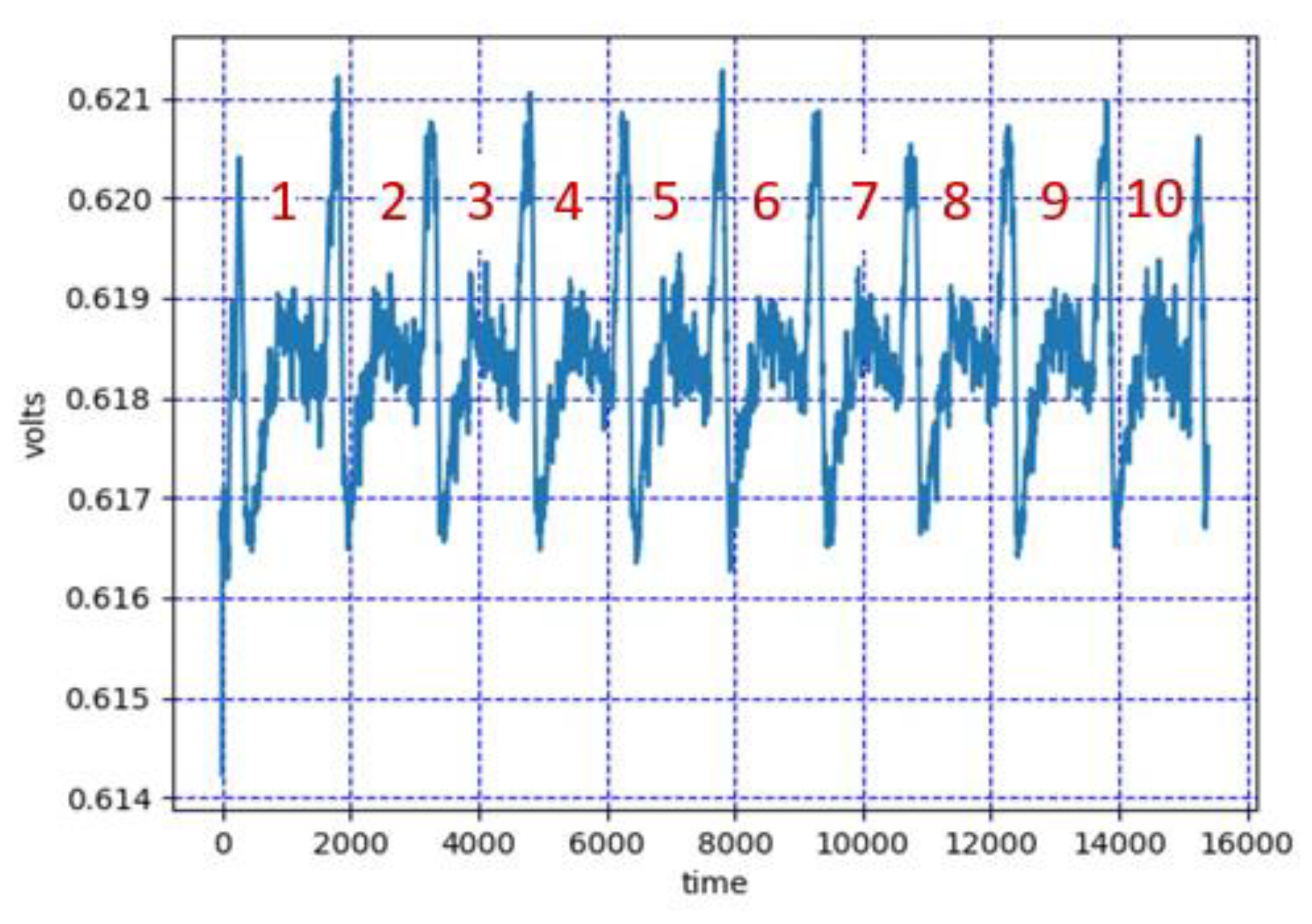
Cryptography | Free Full-Text | Power Side-Channel Attack Analysis: A Review of 20 Years of Study for the Layman
The Book Review Column1 by William Gasarch Department of Computer Science University of Maryland at College Park College Park, M
PDF) A Presentation on VEST Hardware Performance, Chip Area Measurements, Power Consumption Estimates and Benchmarking in Relation to the AES, SHA-256 and SHA-512.